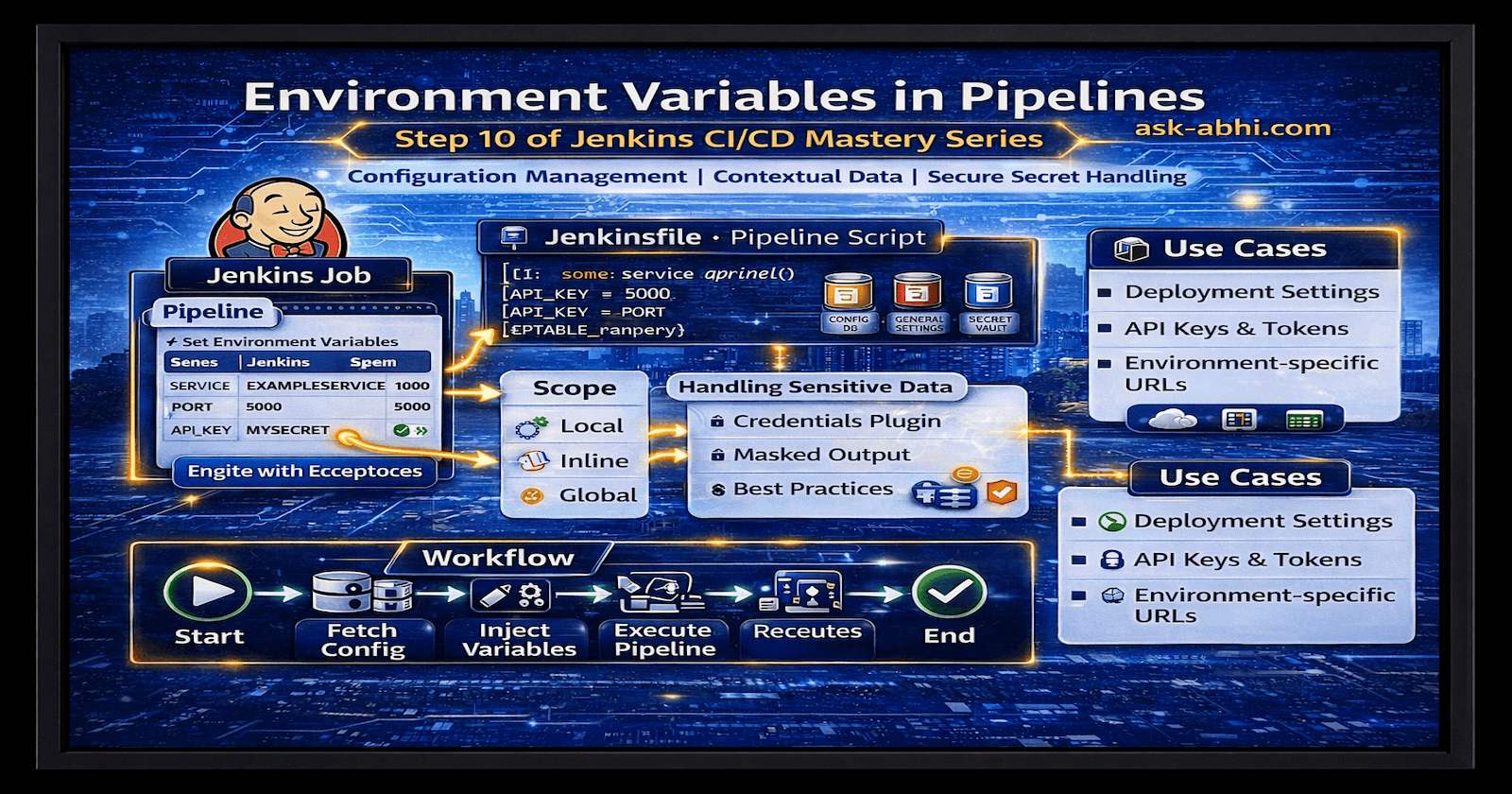
Part 2: Install Jenkins Master, Slave & Tools
AWS EC2 instances with base configuration

What will we set up in this part?
Jenkins Master
Jenkins Slave
EKS
SonarQube
ArgoCD
Trivy
[Note] This project will be implemented in the Singapore region (ap-southeast-1).
Setting up the Jenkins Master
- Spinup AWS EC2 instances with 2CPU, 8GB of RAM (t2.large), and 30 GB of storage, and install Docker on them.

- Open the ports below in the security group of the master machine, and also attach the same security group to the Jenkins worker node (We will create the worker node shortly)

- Install Java
sudo apt update
sudo apt install openjdk-21-jre-headless
java -version
openjdk 21.0.8 2025-07-15
OpenJDK Runtime Environment (build 21.0.8+9-Debian-1)
OpenJDK 64-Bit Server VM (build 21.0.8+9-Debian-1, mixed mode, sharing)
- Install and configure Jenkins (Master machine)
sudo wget -O /etc/yum.repos.d/jenkins.repo \
https://pkg.jenkins.io/rpm-stable/jenkins.repo
sudo dnf upgrade
# Add required dependencies for the Jenkins package
sudo dnf install jenkins
sudo systemctl daemon-reload
- Start Jenkins. You can enable the Jenkins service to
#start at boot with
sudo systemctl enable jenkins
#start the Jenkins service
sudo systemctl start jenkins
#check the status of the Jenkins service
sudo systemctl status Jenkins
Get your password from
sudo cat /var/lib/jenkins/secrets/initialAdminPassword
Now, access the Jenkins Master in your browser using the EC2 public IP on port 8080 and configure it.
Install suggested plugins
Note - If we install suggested pugins then it may slows down Jenkins UI


- Create an admin user to manage Jenkins

- Create AWS IAM-->user-->Create user and then create Access Key
Ex.
Access ID: AKIAZDZTBOHGUD5KKPX3
Secret access key • uPBtoXTLltBRhxoMs8IdfUzQM42LAASsm9nzOgQa
- AWS CLI and configure on Jenkins Master (Setup AWSCLI)
"https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"
sudo apt install unzip
unzip awscliv2.zip
sudo ./aws/install
aws configure
- Check AWS connectivity
aws sts get-caller-identity
- Install kubectl (Master machine) (Setup kubectl )
curl -o kubectl https://amazon-eks.s3.us-west- 2.amazonaws.com/1.19.6/2021-01-05/bin/linux/amd64/kubectl
chmod +x ./kubectl
sudo mv ./kubectl /usr/local/bin
kubectl version --short --client
- Install eksctl (Master machine) (Setup eksctl)
curl --silent --location "https://github.com/weaveworks/eksctl/releases/latest/download/eksctl_$(uname -s)_amd64.tar.gz" | tar xz -C /tmp
sudo mv /tmp/eksctl /usr/local/bin
eksctl version
Create EKS Cluster (Master machine)
Note It may take several minutes to create a new cluster
eksctl create cluster --name=wandercluster \
--region=ap-south-1 \
--version=1.30 \
--without-nodegroup
- Associate IAM OIDC Provider (Master machine)
eksctl utils associate-iam-oidc-provider \
--region ap-south-1 \
--cluster wandercluster \
--approve
- Create Nodegroup (On Jenkins Master)
eksctl create nodegroup --cluster=wandercluster \
--region=ap-southeast-1 \
--name=wandercluster \
--node-type=t2.large \
--nodes=2 \
--nodes-min=2 \
--nodes-max=2 \
--node-volume-size=29 \
--ssh-access \
--ssh-public-key=my-devops-key
Install and configure SonarQube (On the Master node)
docker run -itd --name SonarQube-Server -p 9000:9000 sonarqube:lts-community

- Access the Sonarqube server on:
public-ip-of-jenkins-master:9000
Note- Initial username= admin and password= admin

Install and Configure ArgoCD (On the Jenkins Master)
- Create argocd namespace
kubectl create namespace argocd
- Apply the argocd manifest
kubectl apply -n argocd -f https://raw.githubusercontent.com/argoproj/argo-cd/stable/manifests/install.yaml
- Make sure all pods are running in the argocd namespace
watch kubectl get pods -n argocd

- Install argocd CLI
sudo curl --silent --location -o /usr/local/bin/argocd https://github.com/argoproj/argo cd/releases/download/v2.4.7/argocd-linux-amd64
- Provide executable permission
sudo chmod +x /usr/local/bin/argocd
- Verify argocd

- Check argocd services

- Change the argocd server's service from ClusterIP to NodePort
kubectl patch svc argocd-server -n argocd -p '{"spec": {"type": "NodePort"}}'
Or you can manually edit the manifest file also by going inside it, using this command:

- Confirm service is patched or not
kubectl get svc -n argocd
- Check the port where the ArgoCD server is running and expose it on the security groups of a worker node

port: 31797
- Access it on the browser, click on advance, and proceed with
public-ip-master-node:317979
Note: If you find an error like this in the above image, then run the command below:
kubectl port-forward svc/argocd-server -n argocd 31797:80 --address 0.0.0.0 &
- Page

- Fetch the initial password of the argocd server from Jenkins-ci-master
kubectl -n argocd get secret argocd-initial-admin-secret -o jsonpath="{.data.password}" | base64 -d; echo
Username: admin •
Now, go to User Info and update your argocd password wnx0ZrUozW5oZeDq

Setting up Jenkins Slave node
- Create a new EC2 instance (Jenkins Slave) with 2CPU, 8GB of RAM (t2.large), and 30 GB of storage, and install Java on it

sudo apt update
sudo apt install openjdk-21-jre-headless
java -version
- Attach the IAM role with administrator access
Create an IAM role with administrator access, and attach it to the Jenkins Slave node. Select Jenkins slave EC2 instance --> Actions --> Security --> Modify IAM role
- Configure AWSCLI (Setup AWSCLI)
"https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"
sudo apt install unzip
unzip awscliv2.zip
sudo ./aws/install
aws configure
- **Generate ssh keys (on the master) to set up the Jenkins master-slave relation
**ssh-keygen

- On the Jenkins Slave node, move to the directory(.
ssh) where your ssh keys are generated, and copy the content of the public key and paste to authorized_keys file.


- Now, go to the Jenkins master and navigate to Manage Jenkins --> Nodes, and click on New node
Name: Node • Type: permanent agent
Number of executors: 2
Remote root directory: /home/ubuntu
Labels: Node
Usage: Only build jobs with label expressions matching this node
Launch method: Via ssh
Host: public ip of Jenkins slave
Manage Jenkins---> Credentials: Add --> Kind: ssh username with private key --> ID: Worker --> Description: Worker --> Username: ubuntu --> Private key: Enter directly --> Add Private key
Host Key Verification Strategy: Non-Verifying Verification Strategy
Availability: Keep this agent online as much as possible

Note: the public IP should be the master’s instance-generated private, which is stored in id_ed25519.
- And your Jenkins slave node is added

If any error occurs, open the settings icon of the Node and make changes, then launch the agent again.
- Install Docker (Jenkins slave)
sudo apt install docker.io -y
sudo usermod -aG docker ubuntu && newgrp docker
Install Trivy (On the Jenkins slave)
sudo apt-get install wget apt-transport-https gnupg lsb-release -y
wget -qO - https://aquasecurity.github.io/trivy-repo/deb/public.key | sudo apt-key add -
echo deb https://aquasecurity.github.io/trivy-repo/deb $(lsb_release -sc) main | sudo tee -a /etc/apt/sources.list.d/trivy.list
sudo apt-get update -y
sudo apt-get install trivy -y
Steps to add email notification
If not yet, then -> Go to your Jenkins Master EC2 instance and allow for SMTPS
Now, we need to generate an application password from our Gmail account to authenticate with Jenkins
Open Gmail and go to Manage your Google Account --> Security
Note- [Important] Make sure 2-step verification is on

Search for the App password and create an app password for Jenkins

Note- App password will be in this form "atqw gvjh ifrr wdkf" make sure when you enter in jenkins it should have no space between them like "atqwgvjhifrrwdkf"

- Once the app password is created, go back to Jenkins, Manage Jenkins --> Credentials to add username and password for email notification

- Go back to Manage Jenkins --> System and search for Extended E-mail Notification and set up email notification

- [Important] Enter your Gmail password, which we copied recently, in the password field E-mail Notification --> Advanced

- Verify if the test email was received (Jenkins to Gmail setup successful)

The next configuration is in Part 3