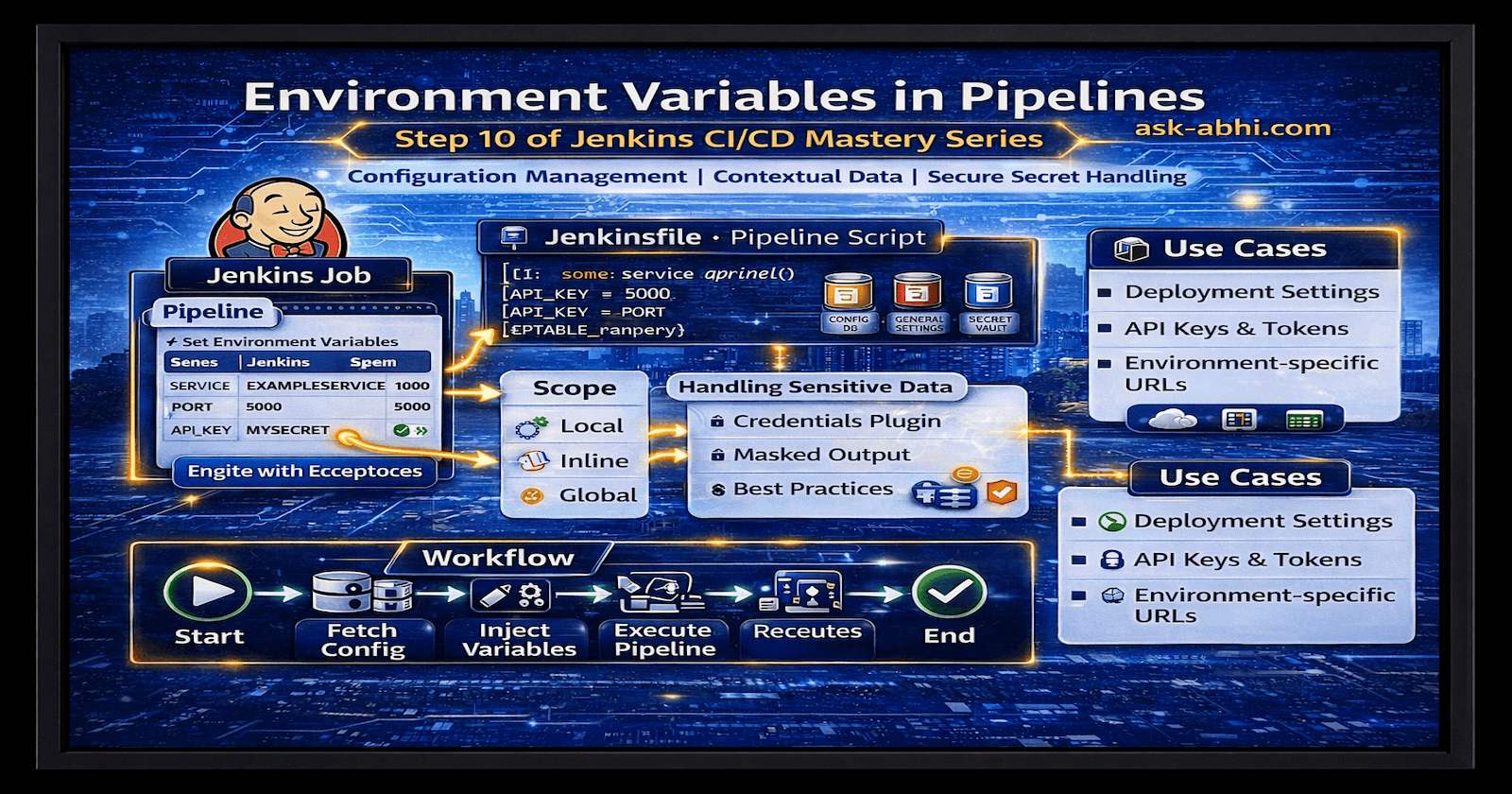
Part 3: Tools Integration with Jenkins
Install plugins, tools, and configuration

Go to Jenkins Master and click on Manage Jenkins --> Plugins --> Available plugins. Install the following plugins:
Install (Some of them get installed during the suggested plugins installation stage at start)
• OWASP (Dependency Check)
• SonarQube Scanner (Quality)
• Git (Code)
• Docker (Containerrization)
• Docker Pipeline
• Pipeline: Stage View
• Pipeline: Job
• Blue Ocean
Fork GitHub Repo: fullstack and share-library
Configure OWASP, move to Manage Jenkins --> Plugins --> Available plugins
After the OWASP plugin is installed, move to Manage Jenkins --> Tools

- Log in to the SonarQube server and create the credentials for Jenkins to integrate with SonarQube
Navigate to Administration --> Security --> Users --> Token


- Now, go to Manage Jenkins --> credentials
SonarQube: Integration
GitHub: Pull shared library and application source code
Docker Hub: to push the image
Create an API credentials for OWASP

- GitHub user name and PAT (as a password)

Create and use an NVD API Key so OWASP can download with the API
Generate API Key. Go to: https://nvd.nist.gov/developers/request-an-api-key
Takes ~10 seconds. Key arrives by email.Add Key to Jenkins Credentials In Jenkins: Manage Jenkins → Credentials → Global → Add Credentials
Type: Secret Text
ID: NVD_API_KEY
Secret: Fix Your API Key: 397ff9xxxxxxxxxxxxxx7b7d1c37

- Go to Manage Jenkins --> Tools and search for SonarQube Scanner installations:

- Now again, go to Manage Jenkins --> System and search for Global Trusted Pipeline Libraries:
Note: Before putting this shared library, Fork GitHub shared repository, and put the project repository URL of your repository.

- Log in to the SonarQube server, go to Administration --> Webhook, and click on create
Public Ip is of Jenkins CI (Master node) and port 8080 because SonarQube is running on it only.

- Now, go to the fullstack GitHub repository (hope you forked already) and under the Automations directory, update the instance-id field on both the updatefrontendnew.sh updatebackendnew.sh with the EKS worker's node instance id

Next...